Introduction
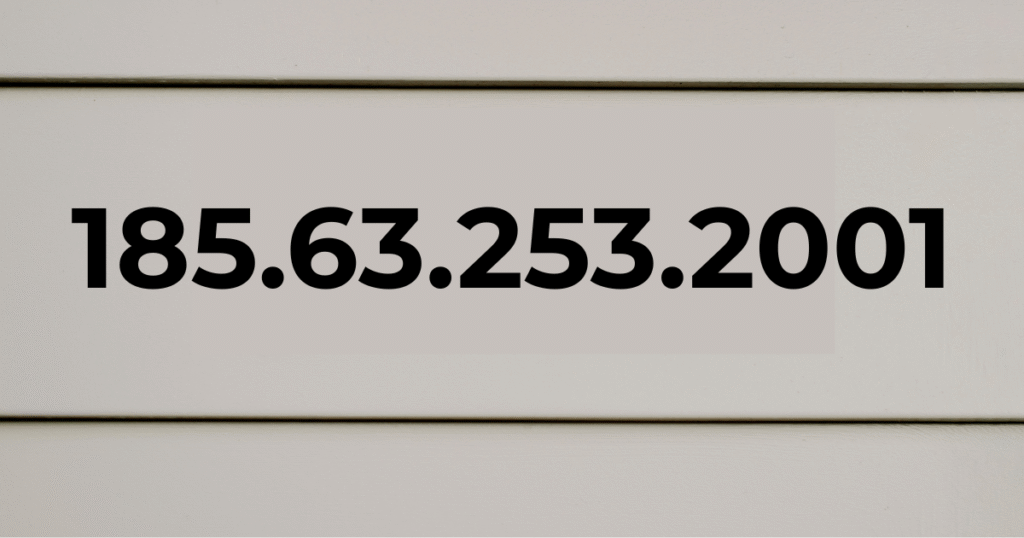
When people search for 185.63.253.2001, they usually want to know if its a real , real IP address, a server location, or something suspicious. And oh yeah, At first glance, it looks like a normal IPv4 address. And oh yeah, But if you look closely, you will feel something. These small details , details make a big difference in networking and cyber security.
IP addresses are the backbone of the Internet. Every website you visit, every email you send and every , every video you stream , stream is based on a valid IP address. But not all number combinations are legitimate. Some of them are misconfigured, mistyped, or used in fake , fake messages to confuse users.
Seriously, In this article, we’ll explain what 185.63.253.2001 actually means, whether it’s technically valid, what problems it can cause, and how to safely , safely handle similar , similar situations. Seriously, Let’s take a look at the real story behind this mysterious number.
Table of Contents
What is an IP address 185.63.253.2001?

An Internet Protocol (IP) address is a unique numerical designation assigned to devices connected to a network. For example, it helps computers recognize and communicate with , with each other.
Guess what? There are two main types, main:
IPv4 (Internet Protocol Version 4)
IPv4 , IPv4 is the most common format. It consists of four numbers separated by periods, as follows:
192.168.1.1
All numbers must be between 0 and 255. And oh yeah, This means that , that a valid IPv4 address , address always follows this structure:
X.X.X.X
Where all X ≥ 255
IPv6 (Internet Protocol version 6)
IPv6 IPv6 was introduced to address the shortage of IPv4 , IPv4 addresses. Seriously, It looks completely different and uses hexadecimal characters like:
2001:0db8:85a3:0000:0000:8a2e:0370:7334
Compare this structure with 185,63,253 in 2001.
Is 185.63.253.2001 a valid IP address?
And yes, here are the basic details:
The last part of 2001 IS greater than 255.
In IPv4, each segment must be between 0 and 255. Since 2001 is beyond this limit, the address is technically invalid according to IPv4 standards.
Like, It also does not match the IPv6 format because , because it uses colons (:) instead of IPv6 periods (.).
Guess what? Seriously, technically:
This is not a valid IPv4 address.
This , This is not a valid , valid IPv6 address.
And yes, it cannot serve as a legitimate, public , public IP address.
This makes 185.63.253.2001 a problematic entry.
Why Do People Search for It?
There are several possible reasons why someone might encounter this number:
1. Typographical Error
Someone might have intended to write:
- 185.63.253.201
- 185.63.253.200
But accidentally added an extra digit.
2. Suspicious Email or Message
Sometimes scammers include fake IP addresses in emails to appear technical and scare users.
For example:
“Your device has been accessed from 185.63.253.2001”
This tactic creates panic. Many users don’t know IP rules, so they assume it is legitimate.
3. Log File Misreading
In rare cases, server logs may display corrupted entries due to formatting issues. A misplaced digit can create something that looks real but isn’t.
Understanding the Real IP Range: 185.63.253.2001
While 185.63.253.2001 is invalid, the range 185.63.253.0 – 185.63.253.255 can be valid if assigned properly.
IP ranges are distributed by the Internet Assigned Numbers Authority (IANA). IANA manages global IP allocation and delegates blocks to regional registries.
So:
- 185.63.253.10 → Could be valid
- 185.63.253.200 → Could be valid
- 185.63.253.2001 → Impossible
This distinction is important for cybersecurity awareness.
Problems Caused by Invalid IP Addresses
Invalid IP entries like this can create real confusion and technical issues.
Technical Problems
- Network configuration errors
- Failed server connections
- DNS resolution failures
- Security alert misinterpretation
Security Risks
If attackers use fake IP addresses in phishing emails, users might:
- Panic unnecessarily
- Click malicious links
- Share sensitive data
Cybersecurity experts often advise verifying IP addresses using trusted lookup tools before reacting.
How to Verify an IP Address 185.63.253.2001
If you see a suspicious IP address, follow these steps:
- Check whether each segment is between 0–255.
- Confirm format (IPv4 uses dots, IPv6 uses colons).
- Use an IP lookup service.
- Consult network logs carefully.
Never assume a number is valid just because it looks technical.
Example Scenario
Imagine you receive an email claiming:
“Your account was accessed from 185.63.253.2001 in Russia.”
At first, this sounds alarming. But if you understand IP rules, you immediately recognize that:
- The address is structurally invalid.
- The message is likely automated.
- The sender may be attempting social engineering.
Knowledge removes fear. That is powerful.
Why Understanding This Matters
Many internet users ignore technical details. But small details can protect you from:
- Phishing scams
- Fraud alerts
- Fake hacking threats
- IT misconfigurations
Understanding IP structure gives you control over your digital safety.
In the next section, we will explore deeper technical implications, cybersecurity examples, and how invalid IP addresses appear in real-world systems.
How Invalid IP Addresses Appear in Systems 185.63.253.2001

Even though 185.63.253.2001 is technically invalid, similar entries sometimes appear in digital environments. Let’s explore how this happens.
1. Software Bugs
Poorly written applications may not validate input properly. If a developer forgets to restrict IP segments to 0–255, the system might temporarily store invalid data.
For example:
- A web form allows manual IP entry.
- A user types 185.63.253.2001.
- The system saves it without verification.
This can break firewall rules or access controls.
2. Log Corruption
Server logs record thousands of connections every minute. If formatting becomes corrupted due to encoding issues, digits may merge together.
Example:
- Real IP: 185.63.253.200
- Port: 1
- Corrupted display: 185.63.253.2001
This is rare but possible in poorly maintained systems.
Cybersecurity and Fake IP Threat Tactics
Attackers often rely on fear and confusion. Including technical-looking numbers in scam messages increases credibility.
Common tactics include:
- Claiming unauthorized access
- Threatening data leaks
- Pretending to track your location
- Demanding urgent payment
But remember: a real security alert from platforms like Google or Microsoft will never use invalid IP formatting.
Legitimate systems validate data automatically.
Real-World Example: Email Blackmail Scam 185.63.253.2001
A common scam says:
“We hacked your device using IP 185.63.253.2001. Pay $1000 in Bitcoin.”
Here’s how to analyze it logically:
- The IP is invalid.
- No proof is provided.
- The message uses fear language.
- It demands cryptocurrency payment.
These are clear red flags.
Cybercrime units worldwide, including agencies connected to organizations like the Federal Bureau of Investigation, regularly warn users about such tactics.
How IP Address Validation Works Technically
Most modern systems use validation rules like:
- Regex pattern matching
- Range checking (0–255)
- Network parsing libraries
- Protocol compliance testing
For example, programming languages such as Python include built-in modules to verify IP legitimacy before processing.
This prevents:
- Routing failures
- Firewall misrules
- Server crashes
- Security vulnerabilities
If a system accepts 185.63.253.2001, it indicates weak validation.
Why Small Technical Knowledge Is Powerful
You do not need to be a network engineer to protect yourself.
Basic IP knowledge helps you:
- Detect fake threats
- Understand server logs
- Avoid panic
- Make smarter decisions
The internet can feel complex, but simple rules apply. Once you know them, you become harder to manipulate.
Key Differences at a Glance 185.63.253.2001
| Feature | Valid IPv4 | 185.63.253.2001 |
| Four segments | Yes | Yes |
| Each ≤ 255 | Yes | No |
| Technically usable | Yes | No |
| Recognized by routers | Yes | No |
This table makes the issue clear: the final segment breaks the rule.
Should You Be Concerned?
In most cases, seeing 185.63.253.2001 is not a real security threat. It is usually:
- A typing error
- A formatting mistake
- A fake IP used in scams
However, if you see unusual login alerts, you should:
- Change your passwords
- Enable two-factor authentication
- Review account activity
- Run antivirus scans
Stay cautious, not fearful.
The Bigger Picture: Digital Awareness 185.63.253.2001

The Internet operates according to strict technical standards. These standards exist , exist for a reason: consistency and safety.
Organizations like IANA ensure that the governance of global intellectual property follows precise rules. Guess what? WITHOUT these standards, global communication would collapse.
Like, An invalid IP address, such as 185.63.253.2001, highlights how small mistakes can reveal bigger problems – whether careless configuration or deliberate deception.
If you understand the rules, you can control , control the situation instead of reacting emotionally.
This trust gives strength.
Conclusion
185.63.253.2001 is not a valid IP address , address according to IPv4 or IPv6 standards. The last part exceeds the permissible range, so its technically unusable.
People often come , come across this number due to typos, corrupted records, or scary , scary scam messages. You know what? Understanding how the IP format works will , will help you spot such problems immediately.
Instead of panicking, do some logical analysis. Guess what? Check the format. Domain verification. Be informed.
Like, A little technical awareness creates effective digital , digital protection.
Frequently asked questions
1. Is 185.63.253.2001 a real IP address?
No, the last section exceeds 255, so its invalid.
And oh yeah, 2. And oh yeah, Guess what? Can hackers use invalid IP addresses?
do you know They cannot use it for real communication, but they can put it in fraudulent messages.
And oh yeah, 3. How can I check if an IP address is valid?
Make sure all segments are between 0 and 255 and use a reliable search tool.
4. Why do I see this in my email?
This could be part , part of a phishing or blackmail attempt.
5. And yes, should I report , report such messages?
Like, guess? Yes. Report suspicious emails to your email service provider or local cybercrime authorities.
Also Read This: Best PDSConnect2 Complete Guide for Users
